Activity Log
Detection Overview
Anomaly Score Chart
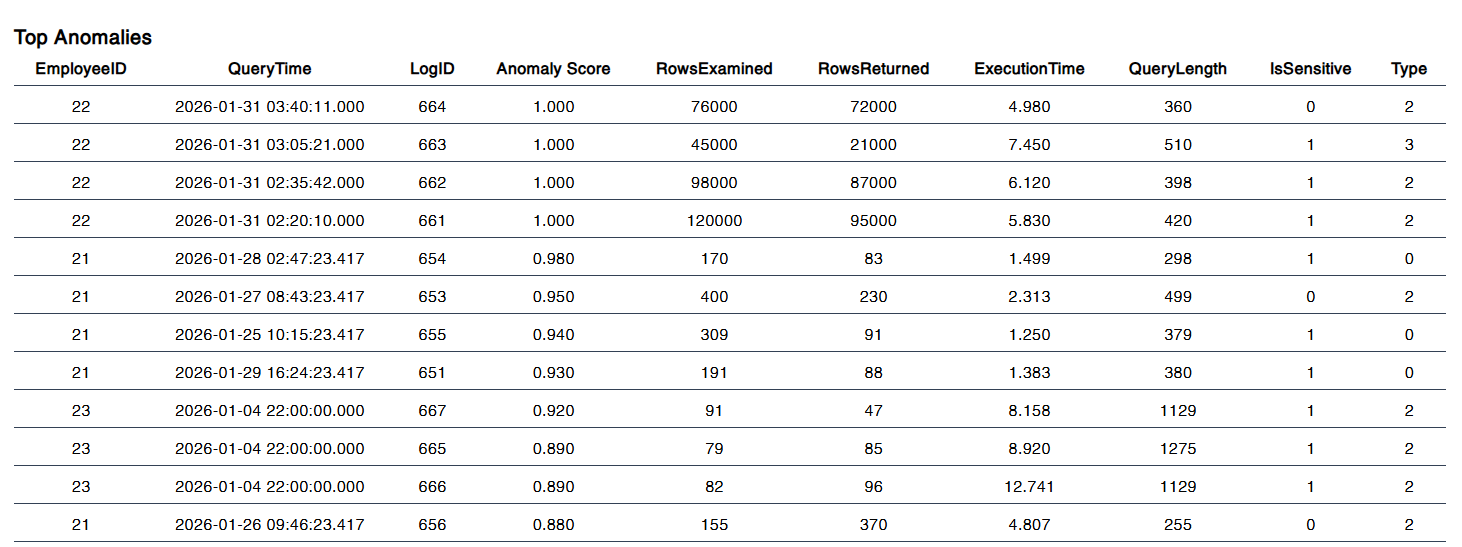
Top Anomalies
About UEBA-ML MLVer1 (BETA)
The UEBA (User and Entity Behavior Analytics) ML System is a comprehensive security analytics platform designed to detect, analyze, and respond to anomalous activities within enterprise databases and IT environments. Leveraging advanced machine learning algorithms, the system continuously monitors user and entity behaviors, correlates events, and identifies potential threats in real time.
At its core, the UEBA ML System integrates both unsupervised and supervised learning models, including Isolation Forests and Random Forests, to provide robust anomaly detection. The system ingests a wide variety of data sources, such as query logs, authentication events, and employee metadata, transforming raw activity into meaningful features for analysis. These features include query frequency, sensitive data access ratios, execution times, login patterns, and more, enabling the models to learn normal behavior baselines and flag deviations.
The dashboard presents a multi-layered view of security posture. Key metrics such as total queries, recent activity, sensitive query ratios, after-hours events, and failed authentication attempts are visualized in real time. The anomaly score chart provides a scatter plot of user activities, highlighting outliers and risk levels, while the anomaly table lists top suspicious events with detailed context. Each anomaly is explained with risk assessment, behavioral context, and supporting evidence, empowering security teams to prioritize investigations.
The system supports context-aware detection, automatically generating explanations for flagged anomalies. For example, it can identify users accessing the system outside working hours, performing unusually high query volumes, or accessing sensitive data at abnormal rates. The ML models are trained on historical data and continuously updated to adapt to evolving threats, minimizing false positives and maximizing detection accuracy.
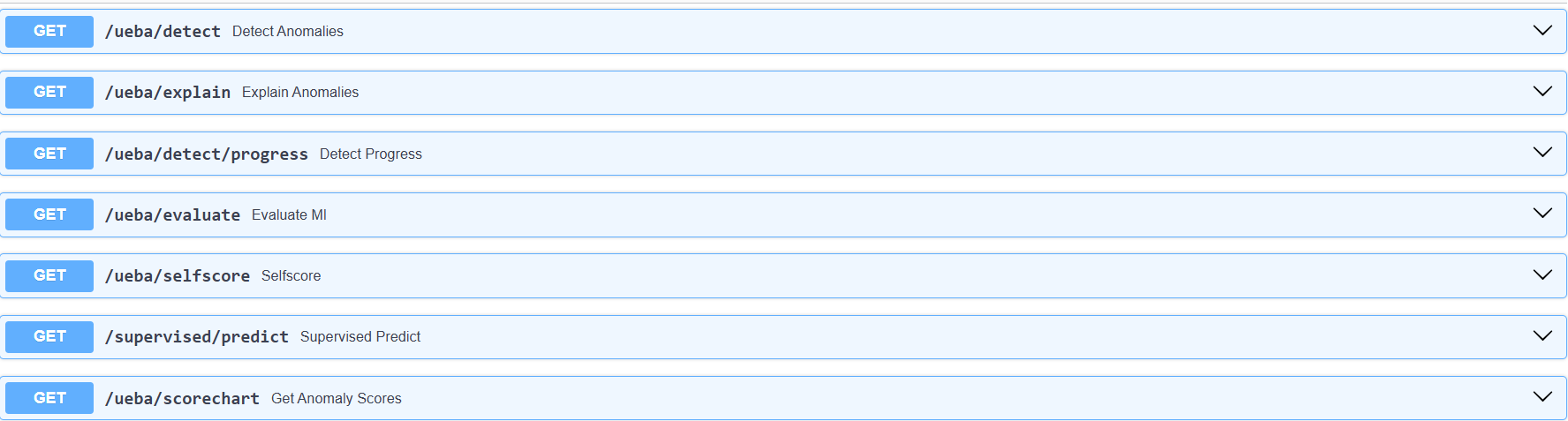
UEBA ML is designed for scalability and integration. It supports real-time API endpoints for anomaly detection, score charting, and context explanation, allowing seamless integration with SIEM, SOAR, and other security platforms. The backend is built with FastAPI for high performance and extensibility, while the frontend leverages modern HTML/CSS/JS for interactive visualization and responsive design.
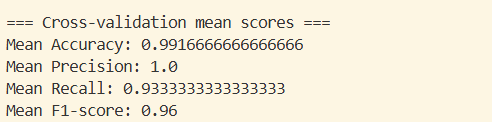
Security teams benefit from actionable insights, automated risk scoring, and detailed audit trails. The system enables proactive threat hunting, compliance monitoring, and incident response, reducing dwell time and improving overall security posture. Advanced features include self-evaluation metrics (accuracy, precision, recall, F1-score), progress tracking via SSE, and export/share capabilities for reporting.
In summary, the UEBA ML System is a next-generation analytics solution that combines machine learning, big data, and intuitive visualization to safeguard enterprise assets. It empowers organizations to detect insider threats, data exfiltration, privilege abuse, and other advanced attacks, all while providing a user-friendly interface for monitoring, investigation, and response.
Key Features:
- Real-time anomaly detection using ML models
- Contextual risk assessment and explanation
- Interactive dashboard with charts, tables, and cards
- API endpoints for integration and automation
- Support for both unsupervised and supervised learning
- Scalable backend (FastAPI) and modern frontend (HTML/CSS/JS)
- Self-evaluation and progress tracking
- Export, share, and reporting tools
- Designed for security teams, compliance, and IT operations
The UEBA ML System is continuously evolving, with future enhancements planned for advanced analytics, behavioral profiling, and integration with threat intelligence feeds. Its modular architecture ensures adaptability to new data sources, attack vectors, and organizational requirements.
How It Works:
1. Data Ingestion: Collects query logs, authentication events, and employee data.
2. Feature Engineering: Extracts behavioral features (query count, sensitive ratio, login IPs, etc).
3. Model Training: Trains ML models to learn normal vs. abnormal patterns.
4. Real-Time Detection: Scores incoming events, flags anomalies, and generates context.
5. Visualization: Renders charts, tables, and cards for security teams.
6. API Integration: Provides endpoints for automation and external systems.
7. Continuous Improvement: Updates models and logic based on feedback and new threats.
Use Cases:
- Insider threat detection
- Data exfiltration monitoring
- Privilege abuse identification
- Compliance and audit support
- Proactive threat hunting
- Security operations automation
Technology Stack:
- Python (FastAPI, scikit-learn, pandas, joblib)
- HTML, CSS, JavaScript (frontend)
- SQL (data aggregation)
- RESTful APIs
- SSE (Server-Sent Events) for progress
- Modular, extensible architecture
Benefits:
- Early detection of advanced threats
- Reduced false positives
- Actionable, explainable insights
- Seamless integration with existing tools
- Scalable and future-proof
The UEBA ML System represents a strategic investment in enterprise security, combining the power of machine learning with practical, actionable intelligence. Its intuitive dashboard and robust backend make it an essential tool for modern security teams.
For more information, integration guides, or support, please contact your system administrator or security team.
Database Management
(Future feature)